Fueled by the myriads of data breaches and hacks, we’re now witnessing the looming end of passwords as they’re fading fast into obscurity. Welcome to the digital world where biometrics and multi-factor authentication (MFA) reign supreme!
According to the Identity Management Institute, one of the biggest problems with basic authentication is that passwords can be guessed or stolen. No doubt, a real headache for security professionals.
In today's day and age, having an online presence has become an essential part of our daily lives. From social media to online shopping and banking, we are always connected to the internet in some way or the other.
We live in a world where hackers and cybercriminals are always on the prowl. And in this world, having a strong (secure) identity is more important than ever. However, the sad reality is that the current slew of identity management solutions is far from secure.
For one, they have a centralized point of failure. Even worse, they’re usually vulnerable to hacks and data privacy breaches. But what exactly is an online identity, you ask?
What Is Internet Identity?
Simply put, it is how you present yourself online. Your online (or digital) identity can include your name, email address, social media profiles, and any other personal information that you choose to put out there. It is your online avatar, a representation of who you are in the digital world.
Thankfully, the DFINITY Foundation has built the Internet Identity (II). II, pronounced “eye-eye,” is your online identity but on steroids. (Steroids, in this case, mean blockchain.) Internet Identity is a highly secure blockchain authentication system supported by the Internet Computer blockchain.
The Internet Identity framework enables you to securely and anonymously sign in to web3 services and dapps (decentralized applications) on the Internet Computer. For example, you can use your II to log in to the Network Nervous System (NNS) dapp, where you can store and stake ICP and participate in the governance of the Internet Computer.
Getting Started with Internet Identity in 3 Simple Steps
To create a session (read: sign in) on the Internet Computer, you’ll first create an Internet Identity anchor.
Each identity anchor has a unique user number, but dapps can’t track your anchor with this number. Instead, Internet Identity creates a pseudonymous identifier for each app you use your anchor to sign in to.
To create your Identity anchor, you will need a device with a security authentication feature (e.g., a security key like Yubikey, a smartphone passcode or locking option, or a biometrics fingerprint or Face ID).
If you use a Windows PC with Windows Hello, you'll have to follow this guide (you don’t need to if you have a security key). Otherwise, follow the five simple steps below to learn how to set up your anchor.
Here’s an explanatory video guide for visual learners to help you get started:
Let’s goooo!
Step 1 — Register Your Device
To quickly start creating an identity anchor, open a supported browser (e.g., Chrome, Safari, or Firefox) and navigate directly to the Internet Identity dapp at identity.ic0.app.
Here, you will be greeted with a welcome screen prompting you to create your identity anchor or manage an existing one. Alternatively, you will be redirected to the Internet Identity welcome screen if you try to access a dapp on the Internet Computer (e.g., the NNS frontend dapp).
Since you’ve never authenticated with II on that device, click Create Identity Anchor. You’ll be prompted to enter your current device’s name (e.g., My iPhone X). Then click Next.
Step 2 — Set Up Your Authentication Device/Method
Once you’ve set your device name, a loading animation will come up and, after, a request from identity.ic0.app to set up your device using the available authentication method.
For example, you’ll receive a prompt from Windows Security to set up your security key if you’re on a Windows PC. You can also use your screen lock passcode if you’re on a smartphone or Face ID on an iPhone.
Once you authenticate, you’ll be taken to the captcha screen. Once you solve the captcha, you’ll (again) receive a request from identity.ic0.app to sign in again. You can either sign in with your device passcode or connect the external security key you authenticated with.
After signing in, you’ll be redirected to a screen containing the ID of your newly created Identity anchor. This number is essential; you’ll need it to sign in to an existing anchor on another device.
If history’s anything to go by, storing sensitive information on your device — or worse, in the cloud — isn’t a good idea, so I’d recommend you write it down in a safe place.
Step 3 — Set Up Account Recovery
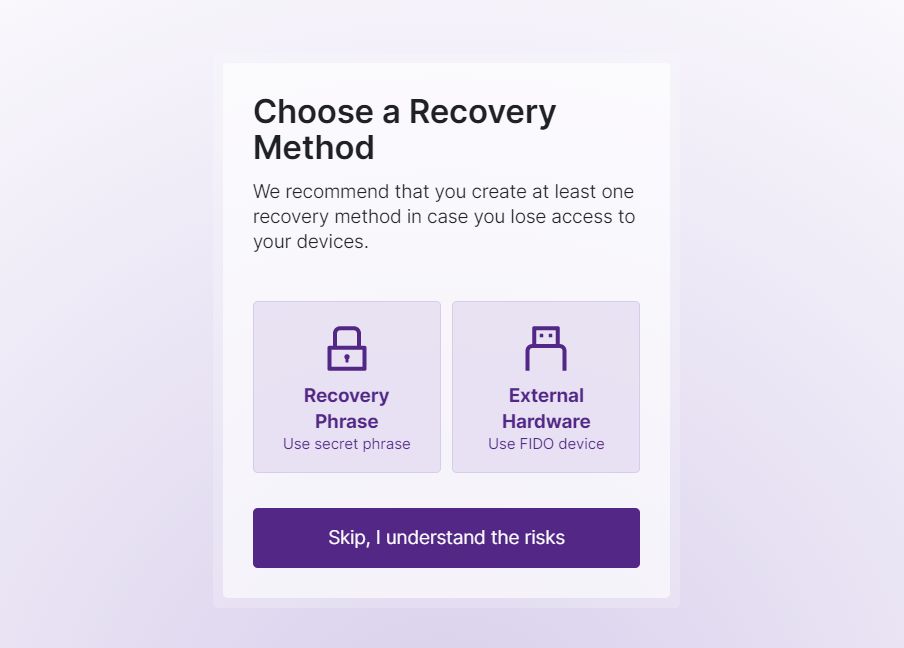
Once you’ve written down your anchor number, click Continue. You’ll be directed to a page where you can add a recovery method to your anchor. Feel free to skip this step if— You know, you really shouldn’t do that unless you’re an Einstein-level gigabrain.
Say you clear your browser history; all your authentication keys will be cleared from the device. This means you’ll no longer be able to access your identity anchor if you do this. Rule of thumb: always add a recovery method when asked to.
(Don’t be that person who missed out on life-changing “f-you” money because they lost access to the Internet Identity anchor. Just don’t.)
Thankfully, II offers more than one way to beef up your identity anchor’s security. For example, you can generate a seed phrase that you can then store safely or add an extra hardware security key for ease of use.
Let’s see how each method works.
Seed Phrase
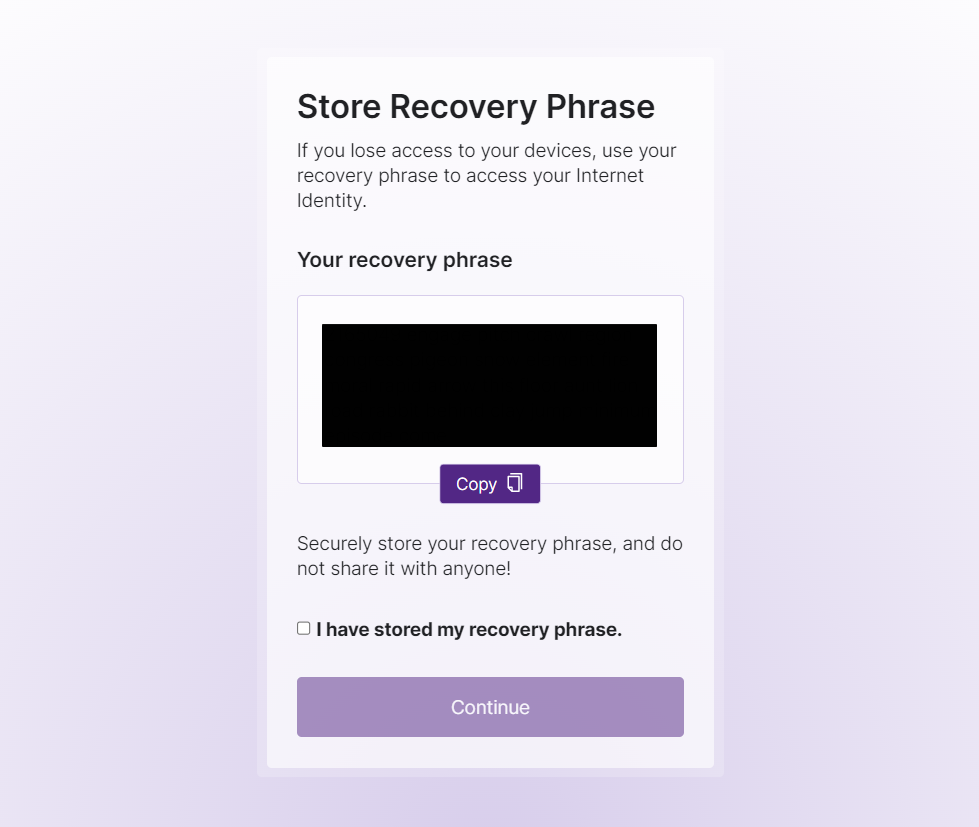
You’ll probably be familiar with seed phrases if you’ve ever used a crypto wallet. If not, read on and learn. A seed phrase (aka recovery or mnemonic phrase) is a sequence of random words that contains the data you’ll need to access or recover your crypto.
In this case, Internet Identity generates a cryptographically-secure seed phrase that you can use to recover your identity anchor. This implies that anyone who knows your seed phrase can control the anchor fully.
Even worse, your crypto balance could be wiped clean if, for instance, you use a wallet with II authentication. Therefore, storing your seed phrase somewhere safe and in a physical location is important. Don’t ever share it with anyone.
Also, II allows you to generate a new seed phrase if your anchor’s ever compromised. The old one becomes effectively invalid, and you’ll have to authenticate to perform the reset. 1000-IQ move right there!
Side note: the first string in your seed phrase is the identity anchor. You will need this number to begin the recovery process.
Security Key
If you don’t trust seed phrases so much, like me, then you can opt for a more secure recovery method: hardware security key. Hardware security keys are physical devices that rely on two-factor authentication to prevent an attacker from accessing your account. They add an extra layer of security to your online identity — the ultimate CSO.
You can use a security key to recover your identity anchor if you can't access your devices. However, using your anchor’s authentication key as your recovery key is not advisable. You can use a dedicated key for maximum security.
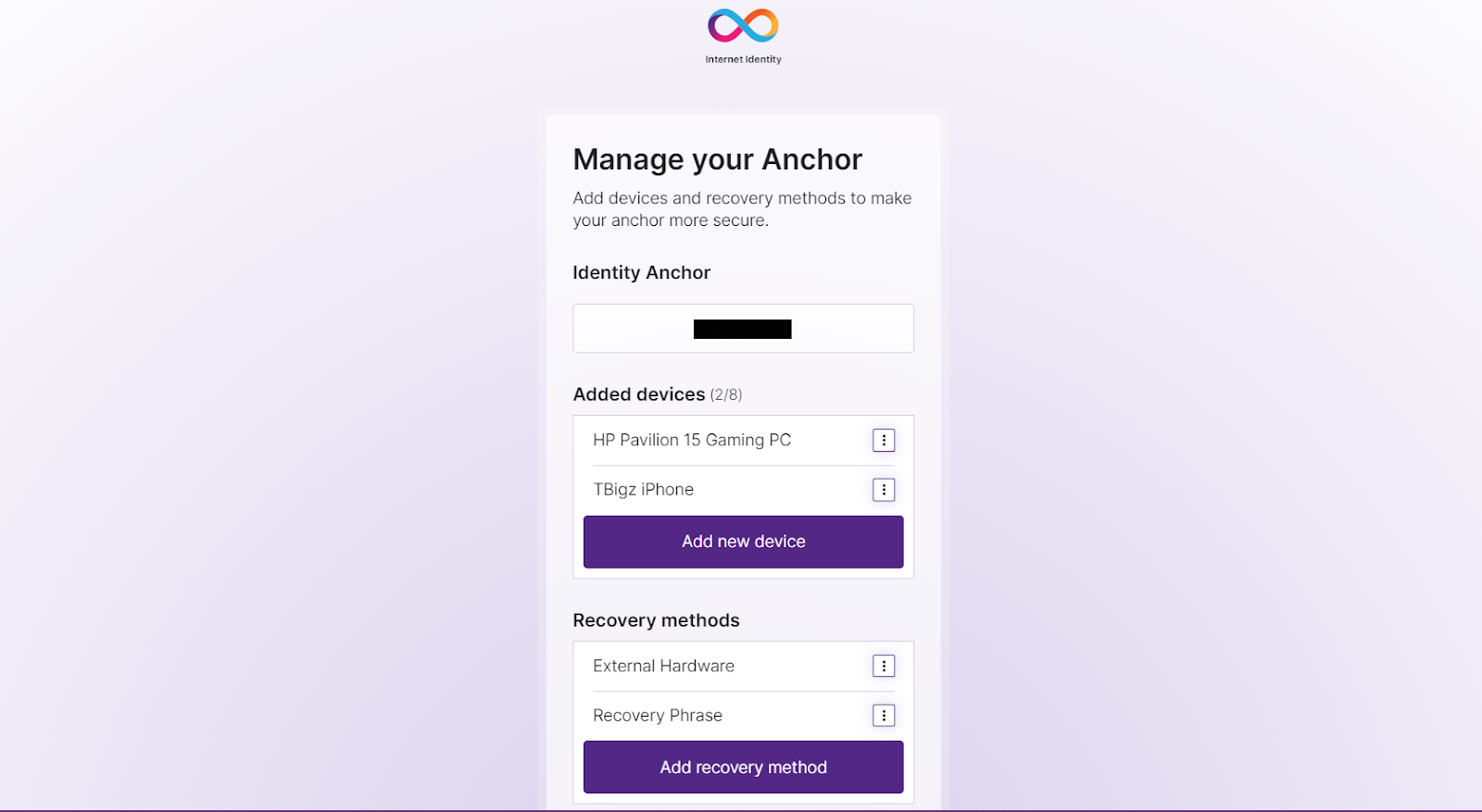
Again, keep your recovery key safe and private. As above, anyone holding this key can control your identity anchor. You will also need to know the identity anchor to begin recovering your identity anchor. You can change your recovery method anytime by logging into identity.ic0.app. You can also manage authorized devices and change your recovery method here.
So you’ve beefed up your anchor’s security with literally multiple checkpoints? Noice, but you’re not there yet. Time to go full Super (Secure) Saiyan by adding a second device!
Internet Identity allows you to add up to eight devices, either a hardware key or another “device device” — your iPhone, for instance. Here’s how:
Add a Second Device to Internet Identity
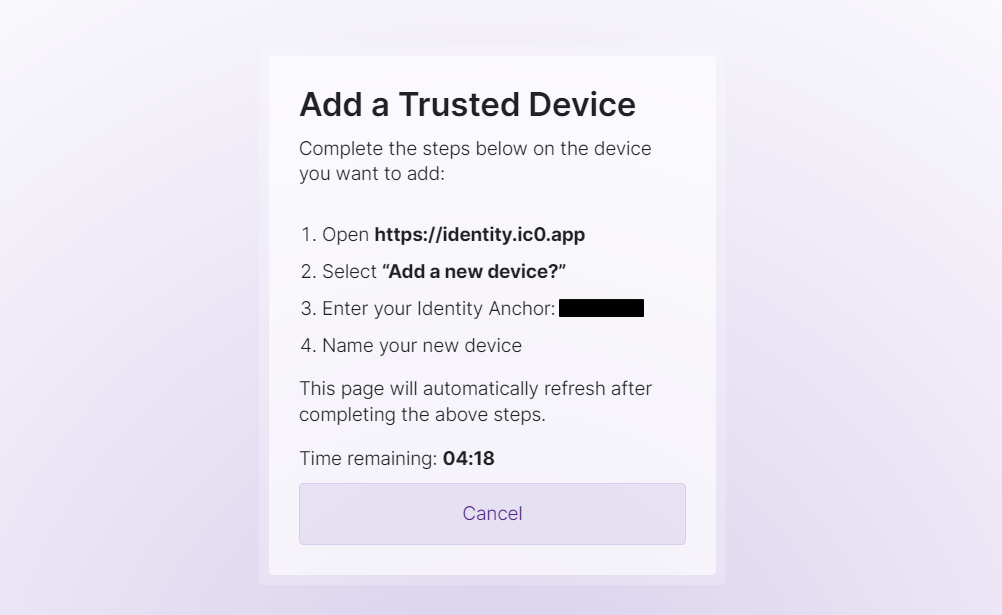
- Sign in to II with your anchor on your primary device and click Add new device. Select Browser.
- Navigate to the Internet Identity dapp on the device you want to add, click Manage Existing and then Add a new device?
- Enter your identity anchor number and click Continue. Enter the name of the device you want to add to your anchor and click Next.
- You’ll be prompted to authenticate the new device with an authentication method. Select your preferred method from the list of available methods and click Continue.
- You’ll be greeted with the following screen or similar:
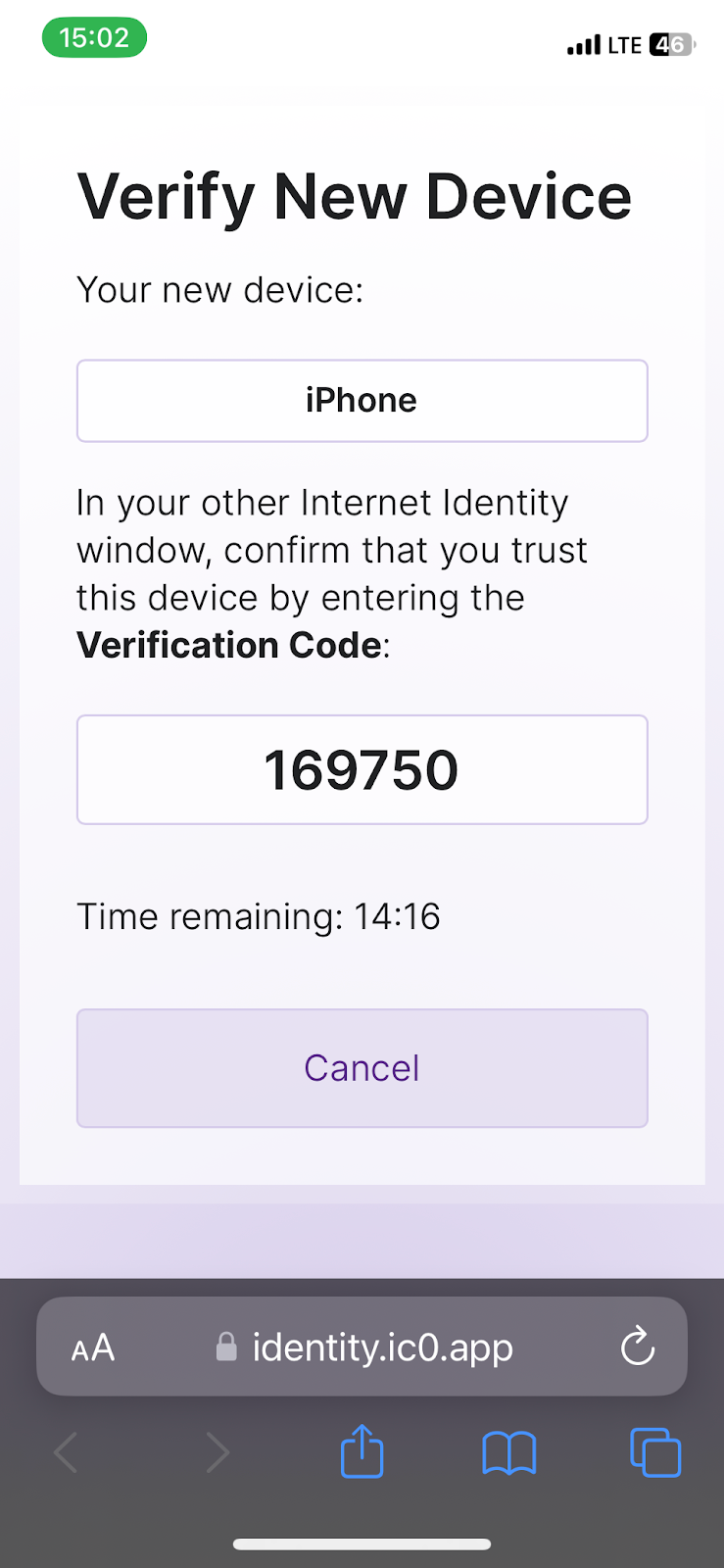
- Enter the verification code displayed on the new device into the input field on the main device before the timer runs out. Click Verify Device.
- Voila! You’ve now added another device to your identity anchor!
Now you can take your Internet Identity for a test drive! Log in and explore the NNS interface or check out DSCVR. Now you're all set to securely and effortlessly participate in the expansive Internet ecosystem.
Closing Thoughts
In conclusion, MFA is the future of modern authentication systems. And Internet Identity is the new face of modern blockchain authentication. Internet Identity is a powerful and secure way to access dapps on the blockchain.
With a novel approach to web3 authentication, you can safely sign on to supported services across multiple devices and authentication methods. By following these simple steps, you can create your Internet Identity and enjoy greater security and privacy when accessing dapps.Visit the Internet Identity dapp to get started, create your Identity anchor, and enjoy the utmost security across decentralized apps and services.
Connect With Us:
Twitter | Telegram | Instagram | Facebook | Email
- Disclaimer: The views and opinions expressed on this website are solely those of the original author and other contributors. These views and opinions do not necessarily represent those of the CoinHustle staff and/or any/all contributors to this site.


Comments are for members only. Join the conversation by subscribing 👇.